Cryptocurrencies are becoming more and more popular every day. As their value increases, so does the risk of theft by hackers. If you own cryptocurrencies, it is essential to protect your wallet from hackers. We will discuss protecting your crypto wallet from hackers and keeping your investments safe.
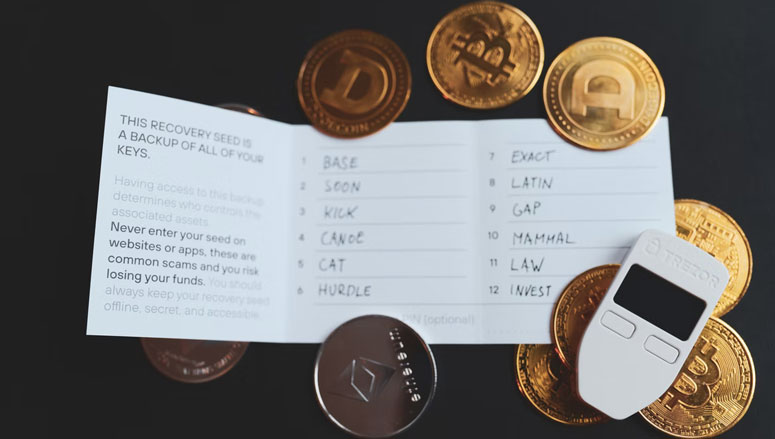
- Use a Hardware Wallet
A hardware wallet is a physical device you purchase that functions as an encrypted crypto wallet. This wallet typically holds multiple cryptocurrencies and can be used on any device, from your computer to smartphone.
- Use HTTPS to Protect Login
One of the most significant risks to your crypto wallet is logging in to check your balance or make a crypto transaction. When you log in, always look for an HTTPS site that begins with HTTPS://. Without this web address feature, hackers can intercept your passwords and log in to your account. Do not use an unsecured login site with HTTP://, even if you are already logged into it.
- Use a Password Generator
Take advantage of a password generator to keep hackers from stealing your valuable cryptocurrencies. There are several password generators available online that will generate passwords for you. These tools create strong passwords that would be almost impossible to crack by a hacker.
- Update Security Settings on Social Media
Social media accounts are often used to send you notifications about your crypto wallet. To protect your wallet’s security on social media sites, ensure you review the settings on each account. Do not allow access to any apps or plug-ins. Hackers can use this type of access to get personal information about you, which they can then access, your crypto wallet.
- Be Careful When Using a Smartphone
Hackers know that many people keep their cryptocurrency wallets on their mobile devices. If you use an unsecured network or public Wi-Fi, hackers can hack into your smartphone and steal all its information. Avoid checking your wallet in public places when possible, and do not use unsecured networks.
- Use VPN When Streaming or Downloading Torrents
Hackers can find out your IP address and use it to compromise your crypto wallet whenever you download or stream anything from the internet. To keep yourself as anonymous as possible, always connect to a Virtual Private Network (VPN) before using the internet. VPNs encrypt all your information so that it is not accessible to anyone else on the internet.
- Use Antivirus Software
It is important to use antivirus on your cryptocurrency wallet. This software will detect and remove any viruses that may attempt to compromise your wallet’s security. It is also good to schedule regular scans with your antivirus software.
- Use 2-Factor Authentication
After you enter your login details, such as a password and username, you’ll have to enter a code sent to your smartphone. This extra layer of protection makes it difficult for hackers to access your crypto wallet, even if they’ve already broken into one of your accounts.
Conclusion
You can keep hackers from stealing your valuable cryptocurrencies by following these steps. Remember to always secure and protect your cryptocurrency wallet and all of your helpful information.